GoSecure Blog
Malicious Chrome Browser Extension Exposed: ChromeBack Leverages Silent Extension Loading
GoSecure Titan Labs received a malicious Chrome extension sample that we are calling ChromeBack (a4424f32a10770b7e486a38823f166ff ) from GoSecure’s Titan Managed Detection and Response (MDR) team. After creating a detection for GoSecure Titan Endpoint Detection & Response (EDR) to ensure that we can identify this threat for our clients, the GoSecure Titan Labs team is ready to spread the word and share how to address this serious issue that some users are already experiencing. The potential impact of ChromeBack is extensive, ranging from browser traffic hijacking and ad-redirection to deactivation of other extensions and even the activation of developer mode without the user’s knowledge.
How CI/CD Enabled the GoSecure Titan Platform to Respond to Log4j Vulnerabilities
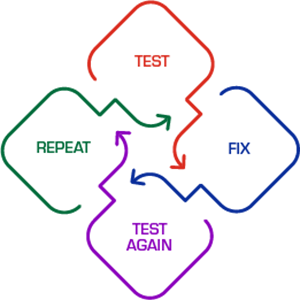
 Log4j was an eye opener for many here at GoSecure. Not from a technology or security perspective, we have that covered in spades; but just how quickly the GoSecure Titan team can respond and remediate a vulnerability in a dependency. We are starting to appreciate the speed CI/CD (continuous integration / continuous delivery) has brought to the normal development cycle for handling bugs and bringing new features to market.
Log4j was an eye opener for many here at GoSecure. Not from a technology or security perspective, we have that covered in spades; but just how quickly the GoSecure Titan team can respond and remediate a vulnerability in a dependency. We are starting to appreciate the speed CI/CD (continuous integration / continuous delivery) has brought to the normal development cycle for handling bugs and bringing new features to market.
Internally, we have been touting how great a full CI/CD pipeline is for increasing our development velocity, but no one had considered what it meant to vulnerability response times. It was an eye opener for the GoSecure Titan team, and in a good way! So, I would like to share our journey that led to this, which all culminated in a fast response to the Log4j vulnerabilities.
Interview with an Ethical Hacker – The Inside Scoop on Purple Team Services
 GoSecure Ethical Hacker Maxime Nadeau shares his perspective on the quickly growing, industry capability that delivers fast and long-lasting security improvements through a collaborative engagement.
GoSecure Ethical Hacker Maxime Nadeau shares his perspective on the quickly growing, industry capability that delivers fast and long-lasting security improvements through a collaborative engagement.
GoSecure Titan Labs Exposes Fake Banking Websites
 GoSecure Titan Labs team has discovered a significant number of fake banking websites through samples obtained from the GoSecure Titan Inbox Detection & Response solution. Unlike conventional phishing websites which impersonate the website of specific banks to steal user’s login details, these sites attempt to portray themselves as the website and/or portal of a fictitious bank.
GoSecure Titan Labs team has discovered a significant number of fake banking websites through samples obtained from the GoSecure Titan Inbox Detection & Response solution. Unlike conventional phishing websites which impersonate the website of specific banks to steal user’s login details, these sites attempt to portray themselves as the website and/or portal of a fictitious bank.
In this blog, the GoSecure Titan Labs team will detail their “Operation Bankroll” investigation, expose several fake bank websites, explain the expanding problem with fake bank domains and provide practical tips to avoid falling victim to the scams.
Capturing RDP NetNTLMv2 Hashes: Attack details and a Technical How-To Guide
The GoSecure Titan Labs team saw an opportunity to further explore the topic of hash capturing (which is a must in the arsenal of any offensive team). This blog will examine RDP security modes, how they work and how to put that into action to capture NetNTLMv2 hashes via the RDP protocol using PyRDP—a library created by GoSecure. This effort started with a project during the annual month-long Hacktoberfest which led to several improvements to PyRDP. Among those improvements, we made it easier for the user to capture NetNTLMv2 hashes.



