 Author: Philippe Arteau
Author: Philippe Arteau
In the past six months, we have been working on a new static analysis tool for the .NET ecosystem called Roslyn Security Guard. It is a Visual Studio extension that analyzes C# code. It was first released at Black Hat USA this year. This article will cover the latest milestone reached which brings a new taint analysis mechanism and the introduction of automated code fixes.
Roslyn does provide a small subset of security checks. This small subset will not satisfy security analysts or developers doing in-depth security code reviews. The goal of the project is to complement the built-in Microsoft rules.
Taint Analysis
Taint analysis is the capability to track variables in the code flow and trace variable coming from user input (considered tainted). If a variable can be controlled by an external user, it will cause problems if it is passed to a dangerous API such as a method accepting SQL queries. This helps reduce false positives reported by identifying correct usage of risky APIs.
Here is a simple example of an SQL query that is not vulnerable to SQL injection but, it requires context analysis to determine that it is safe to use.
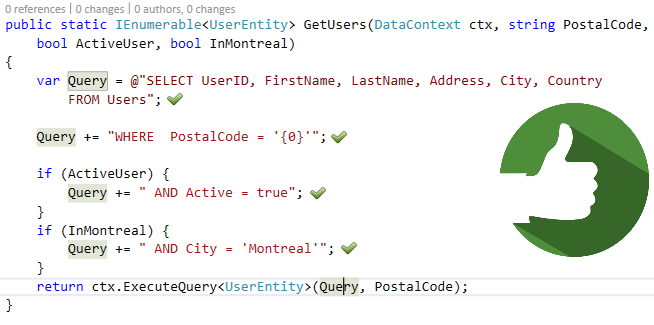 Safe SQL Query (No issue is reported)
Safe SQL Query (No issue is reported)
On the other hand, the following sample will be marked as vulnerable because the parameter PostalCode is concatenated to the query string. Any potentially unsafe value will trigger a vulnerability.
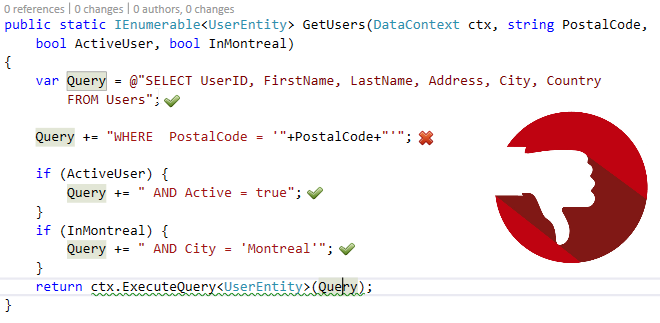 Unsafe SQL Query (Issue is reported)
Unsafe SQL Query (Issue is reported)
The taint analysis engine is reused in a similar fashion to find an hard-coded password. Constant variables are tracked to see if they are assigned to a password parameter or field. Analyzers were created to find obvious password fields in standard well-known APIs. Additionally, heuristics are used to look for password fields in proprietary APIs.
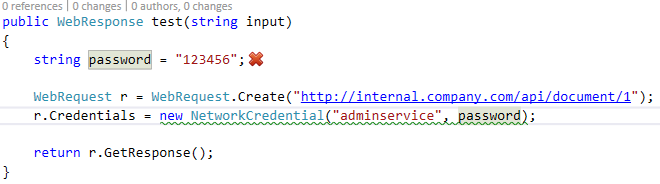 Hard-Coded Password
Hard-Coded Password
Automated Code Fixes
Code fixes are refactoring hints to fix diagnostics found by Roslyn analyzers. In the context of security, it means that developers get an immediate course of action to fix a vulnerability at the moment it was created. Security vulnerabilities can often be abstract and dubious. This will help developers get the code right during implementation and patch vulnerabilities quicker.
 Code Fix proposing the addition of Secure and HttpOnly flag to browser cookies.
Code Fix proposing the addition of Secure and HttpOnly flag to browser cookies.
Open for contributions
The project is open to contributions. You can suggest or contribute new analyzer idea. The project is designed to make signature addition easy. The dangerours APIs are configured in a YAML file. If you need the support of a library, you can add an entry as follows:
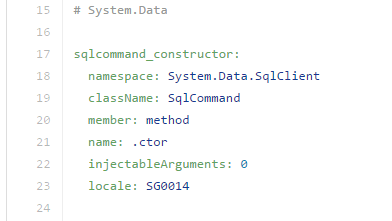 Excerpt from the dangerous API configuration
Excerpt from the dangerous API configurationConclusion & Future plans
You can download the extension from Visual Studio Gallery. If you encounter any problem, you can report them on the Github project.
Both components presented – Taint analysis and Automated Code Fix – are still under active development. The features presented today are a small subset of the project’s roadmap. You can expect major improvements in the upcoming months.
References
Roslyn Security Guard : Official website
Roslyn Security Guard’s Github project : Place to contribute to the project
Icons Designed by Kreativkolors – Freepik.com : Thumbs icons used in the article


CAS D'UTILISATION
Cyberrisques
Mesures de sécurité basées sur les risques
Sociétés de financement par capitaux propres
Prendre des décisions éclairées
Sécurité des données sensibles
Protéger les informations sensibles
Conformité en matière de cybersécurité
Respecter les obligations réglementaires
Cyberassurance
Une stratégie précieuse de gestion des risques
Rançongiciels
Combattre les rançongiciels grâce à une sécurité innovante
Attaques de type « zero-day »
Arrêter les exploits de type « zero-day » grâce à une protection avancée
Consolider, évoluer et prospérer
Prenez de l'avance et gagnez la course avec la Plateforme GoSecure TitanMC.
24/7 MXDR
Détection et réponse sur les terminaux GoSecure TitanMC (EDR)
Antivirus de nouvelle génération GoSecure TitanMC (NGAV)
Surveillance des événements liés aux informations de sécurité GoSecure TitanMC (SIEM)
Détection et réponse des boîtes de messagerie GoSecure TitanMC (IDR)
Intelligence GoSecure TitanMC
Notre SOC
Défense proactive, 24h/24, 7j/7