GoSecure Titan Labs discovered a stored cross-site scripting (XSS) vulnerability in IBM Content Navigator. Users are strongly advised to upgrade to version 3.0.9 or above. This blog post details the vulnerability, its impact and provides a proof of concept for exploitation.
 IBM Content Navigator is, according to IBM, a flexible, full featured content management solution. The application is vulnerable to Stored Cross-Site Scripting (XSS) injections via its file upload functionality. An attacker may be able to upload malicious HTML content and trick the user into clicking on the malicious link generated by the application or preview the document that contains the JavaScript code. Once triggered, the malicious JavaScript code is executed in the victim’s browser.
IBM Content Navigator is, according to IBM, a flexible, full featured content management solution. The application is vulnerable to Stored Cross-Site Scripting (XSS) injections via its file upload functionality. An attacker may be able to upload malicious HTML content and trick the user into clicking on the malicious link generated by the application or preview the document that contains the JavaScript code. Once triggered, the malicious JavaScript code is executed in the victim’s browser.
Impact
IBM rated this vulnerability with a CVSS 3.0 rating of 6.4 (CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:C/C:L/I:L/A:N) which results in a medium severity vulnerability.
Exploitation of this issue could allow attackers to execute code in the victim’s browser that could lead to accessing certain types of data such as cookies or credentials within a trusted session.
While exploitation of this issue does require authentication to the platform using a low privilege account and interaction of the targeted user with the malicious link generated by the platform, the technical requirements remain low since only basic JavaScript coding knowledge is required to perform the attack.
Technical Analysis
In the IBM Content Navigator platform, users can upload files that will then be served by the platform. To exploit the vulnerability associated with this feature, an attacker needs to upload a malicious file containing HTML content via the file upload functionality. Successful exploitation could allow the attacker to obtain the victim’s session cookie or conduct social engineering attacks.
For instance, a valid attack scenario would be to clone the application’s login page within the malicious HTML file. Once opened it would alert the end-user that their session has expired prompting them to enter their credentials and therefore potentially lead to account takeover.
Exploitation of this vulnerability can be achieved using the following steps:
1st Step: Create the HTML file containing the malicious payload. For this demonstration, the following payload was used:
<html> <head>POC Cookie Grabber</head> <body> <img src=# onerror=alert(document.cookie)> "><iframe/src=javascript:alert(document.cookie)> </body> </html>
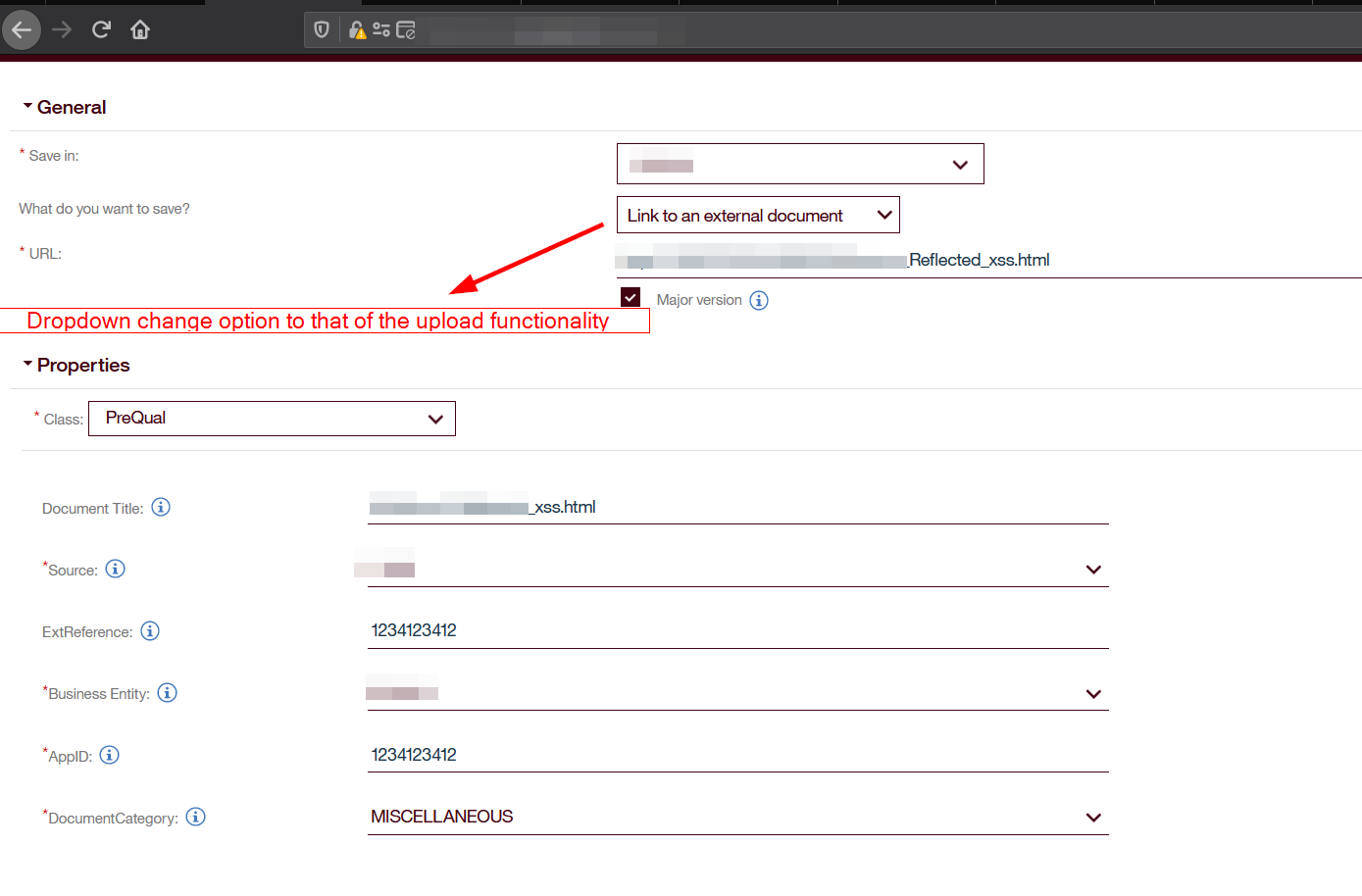
2nd Step: Click on the drop-down icon to select the upload file option.
3rd Step: Upload the file
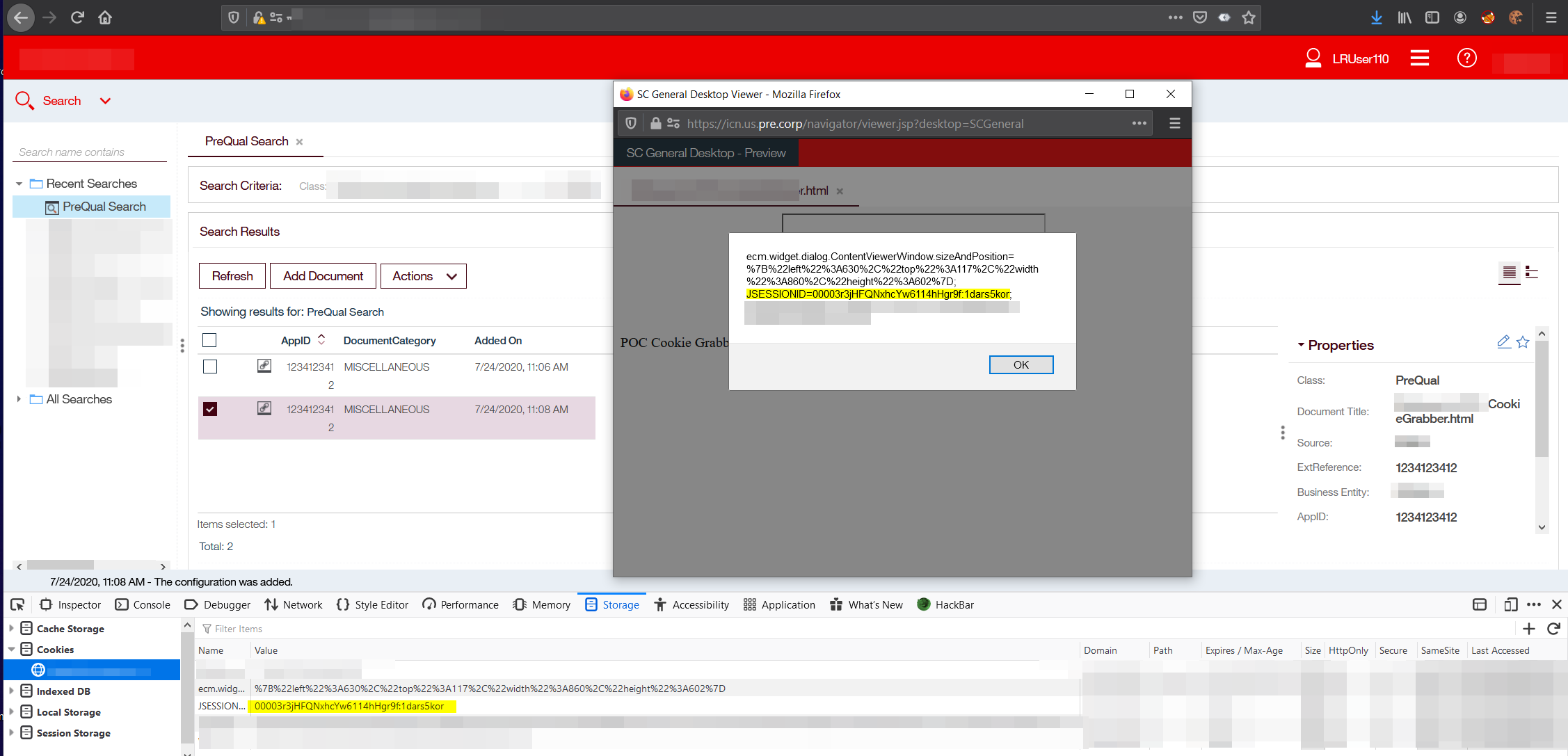
Search for the file via the AppID assigned in step 2 and then select the result for the search AppID and either « Preview » or « Open in a new tab ».
This will display the XSS and user’s cookie.
Mitigation
To ensure adequate protection against this vulnerability, update IBM Content Navigator to version 3.0.9 and above.
If this is not currently possible, as mentioned by IBM, the IBM Content Navigator viewer map can be configured to prevent users from opening or previewing certain types of documents as described in this article: https://www-03preprod.ibm.com/support/knowledgecenter/SSEUEX_3.0.8/com.ibm.installingeuc.doc/eucco011.htm
Conclusion
Vulnerabilities like Cross-Site Scripting, caused by a lack of user-input filtering, are well known but are still very prevalent. By using well-known security solutions, following secure development practices, and ensuring that commercial applications are always up to date, you can avoid vulnerabilities like these and keep your application secure.
This vulnerability was assigned CVE-2020-4757 and has been disclosed to the vendor following our responsible disclosure process. The IBM Security Bulletin is available here.
Vulnerability identified and documented by Olivier Laflamme and blog post by Louis-Philippe Frenette Blais.


CAS D'UTILISATION
Cyberrisques
Mesures de sécurité basées sur les risques
Sociétés de financement par capitaux propres
Prendre des décisions éclairées
Sécurité des données sensibles
Protéger les informations sensibles
Conformité en matière de cybersécurité
Respecter les obligations réglementaires
Cyberassurance
Une stratégie précieuse de gestion des risques
Rançongiciels
Combattre les rançongiciels grâce à une sécurité innovante
Attaques de type « zero-day »
Arrêter les exploits de type « zero-day » grâce à une protection avancée
Consolider, évoluer et prospérer
Prenez de l'avance et gagnez la course avec la Plateforme GoSecure TitanMC.
24/7 MXDR
Détection et réponse sur les terminaux GoSecure TitanMC (EDR)
Antivirus de nouvelle génération GoSecure TitanMC (NGAV)
Surveillance des événements liés aux informations de sécurité GoSecure TitanMC (SIEM)
Détection et réponse des boîtes de messagerie GoSecure TitanMC (IDR)
Intelligence GoSecure TitanMC
Notre SOC
Défense proactive, 24h/24, 7j/7